Ako Ransomware Sample Download
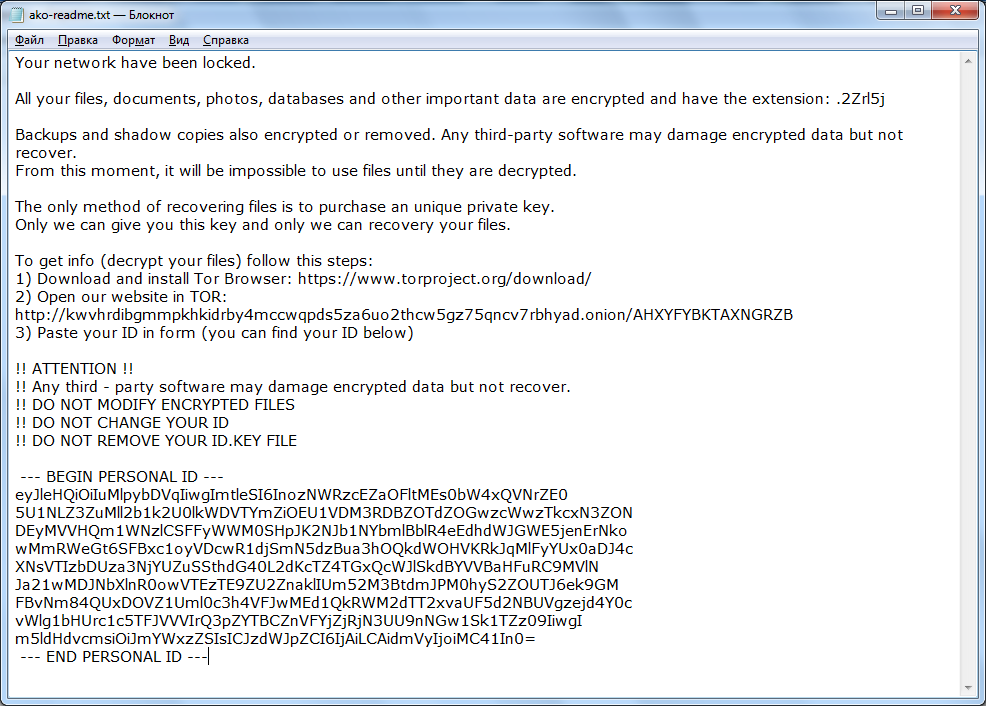
Ako ransomware encrypts the data of computers on the local network running Windows (including Windows 10) using AES, and then requires a ransom of 0.5 to 1 BTC in order to return the files. Ransom amount varies from case to case. Starting in May 2020, the malicious actors behind Ako Ransomware began to publish stolen data on a special site accessiable via TOR http://kwvhrdibgmmpkhkidrby4mccwqpds5za6uo2thcw5gz75qncv7rbhyad.onion in order to increase pressure on the victim. To do this, ransomware operators begin to steal data before encrypting files. In some cases, they even began to demand an additional fee to delete the stolen data.
Update: A new version of Ako is release named Ranzy Locker Ransomware.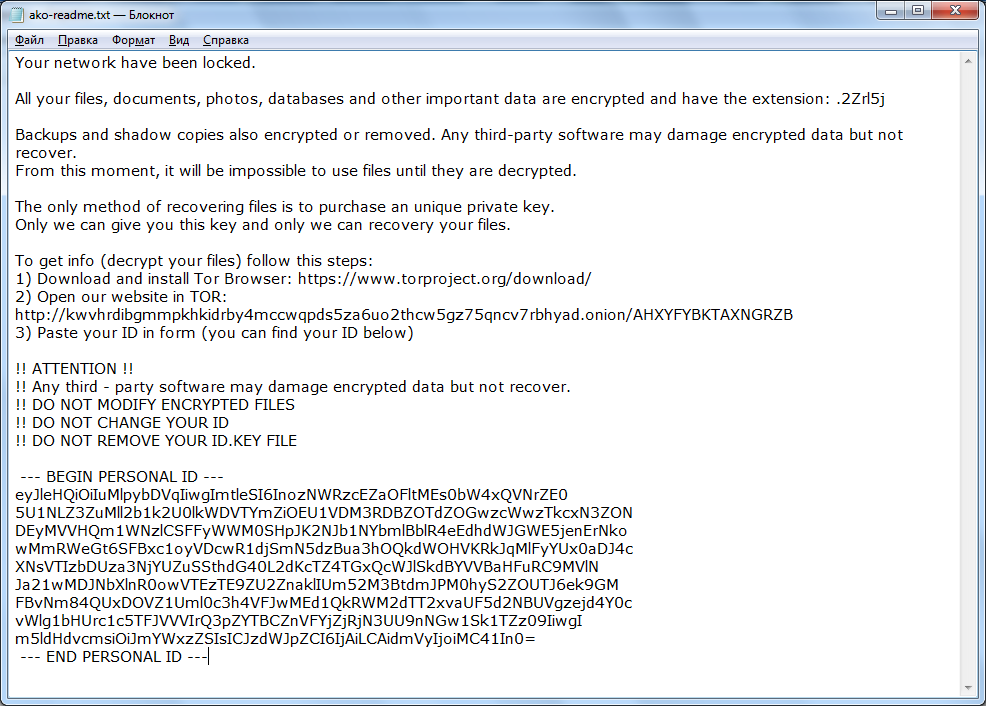
Ako Ransomware borrows techniques from MedusaLocker which made it believe to some researchers that it might be a new version of MedusaLocker which they dubbed as MedusaReborn. But the author categorically denied any link with MedusaLocker.
Update: A new version of Ako is release named Ranzy Locker Ransomware.
Ako Ransomware borrows techniques from MedusaLocker which made it believe to some researchers that it might be a new version of MedusaLocker which they dubbed as MedusaReborn. But the author categorically denied any link with MedusaLocker.
Ako Ransomware Download

Click to Load Comments
