tRat Malware Sample Download
tRat is a modular delphi remote access trojan from the threat actor TA505. TA505 was previously responsible for Dridex and Locky campaigns. tRAT malicious word document present itself as if it is written in old verion of Word and the user have to enable the macro to view the content. Once the macro are enabled a tRAT is downloaded. Malicious binary is stored in C:UsersAppDataRoamingAdobeFlash PlayerServicesFrame Hostfhost.exe . Next, tRat creates a LNK file in the Startup directory that executes the binary on startup C:UsersAppDataRoamingMicrosoftWindowsStart MenuProgramsStartupbfhost.lnk . Sample Malicious Microsoft Word Document.
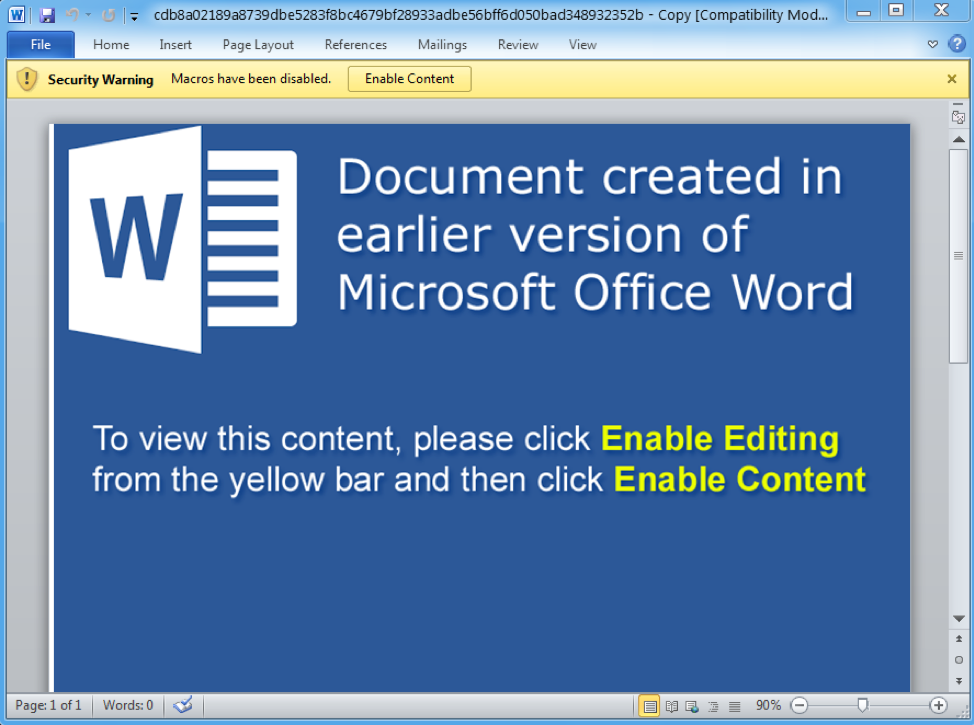


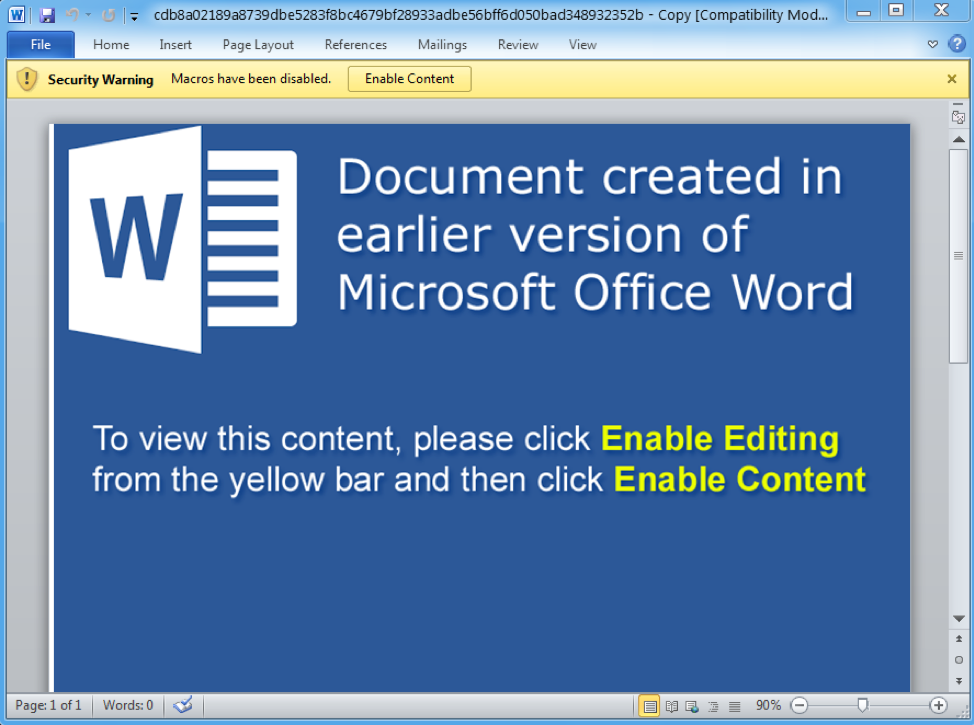
tRAT Word Document Signatures
Family: Trojan:Win32/Tiggre!rfn MD5: 5021196ad2fe329e769efb33e97af19d SHA256: cdb8a02189a8739dbe5283f8bc4679bf28933adbe56bff6d050bad348932352b
tRAT Word Document Download

tRAT Malware Signatures
Family: Trojan:Win32/Occamy.C MD5: 6322275a1f81abaa51b973551552fee0 SHA256: a8d47832404d91816f9be936575a5bacc3476bdff6e7a7f7176fd8d28cf002a5
tRAT Malware Download

Click to Load Comments


